
Exploring the Theory of Information Worlds: A Content Analysis of Its Applications and Developments

Jisue Lee (Department of Library & Information Science, Chonnam National University, Gwangju, Korea)

Sungjae Park (Knowledge and Information Culture Track, Hansung University, Seoul, Korea)

Abstract
This study explores the applications and developments of the theory of information worlds (TIW), developed by Burnett and Jaeger (2008), Jaeger and Burnett (2010), in peer-reviewed research published between 2008 and 2023. Building on the previous systematic review by Park et al. (2022), a qualitative content analysis was conducted on 27 articles that employed TIW at substantial theoretical levels, including theory application, theory conversation, and theory generation. The findings reveal that TIW serves as a robust and scalable theoretical framework, applied across diverse contexts and methodological approaches, often integrated with qualitative and mixed methods. The core concepts of normative information behavior and information value were most frequently employed and concepts such as social types were less frequently applied, indicating potential areas for further theoretical refinement. TIW has also informed new theoretical contributions, including a framework of information access in local communities and a theory of local information landscapes, and has been used in conjunction with complementary theories across disciplines. While criticisms regarding its limited treatment of individual agency and affective dimensions have been raised, recent theoretical developments incorporating cognitive and signification domains into the framework have sought to address these limitations. This study contributes to understanding the role and evolution of LIS theory and highlights the potential of TIW for future theoretical advancement and interdisciplinary application.
- keywords
- theory of information worlds, theory application, theory development, theory generation, content analysis
1. INTRODUCTION
The field of library and information science or studies (LIS) has been criticized for its lack of theory development, as well as reliance on theories from other disciplines. McKechnie et al. (2001), Pettigrew and McKechnie (2001), and Kim and Jeong (2006) found that the use of theory in LIS research in the 1990s and early 2000s was trending upward. However, Pettigrew and McKechnie (2001) identified notable use of theories from other disciplines and a lack of use of theories from within LIS. Additionally, Kim and Jeong (2006) noted a decline in articles focusing specifically on theory development. A decline in theory use in LIS conference papers (Vakkari, 2008; VanScoy et al., 2022) and LIS research and professional articles (Julien et al., 2011) has also been noted. Other research has pointed to the increased use of theories from external disciplines, prompting calls to reinforce theory use and development from within LIS (Julien et al., 2011; Kassim, 2024; McKechnie et al., 2001; Pettigrew & McKechnie, 2001; Ukwoma & Ngulube, 2021; VanScoy et al., 2022).
To address these challenges, the present authors decided to explore and describe the use and development of a theory native to LIS: Burnett and Jaeger (2008)’s and Jaeger and Burnett (2010)’s theory of information worlds (TIW hereafter). Burnett and Jaeger (2008; 2011)’s and Jaeger and Burnett (2010)’s TIW characterizes the social contexts of information behavior through five core concepts, as described in the literature review. This study represents the third study in the series. In the first study, Park (2022) explored the use of TIW across 14 doctoral dissertations and found that TIW is often used with qualitative methods, with the interactions between the core concepts helping to describe and explain individuals’ social information worlds. The second study, Park et al. (2022) expanded on the first through a systematic review of peer-reviewed research articles and found a similar trend of TIW and qualitative methods. They also found that while the adoption of TIW is trending upwards in LIS and across disciplines among scholars worldwide, relative awareness and adoption of TIW appears to be low.
The purpose of this study is to continue exploring and describing how and in what ways TIW has been applied and developed in peer-reviewed research articles. The previous study by Park et al. (2022) primarily describes quantitative trends, such as author affiliations and disciplines, publication venues, author keywords, research method types, and sample populations. This study iterates on the previous by re-using and updating the original sample and revising the analytical framework, and differs by looking more closely at how and why TIW has been applied and developed, as well as how it has informed LIS theory development and scholarship through qualitative content analysis. The qualitative content analysis of this study allows for a more nuanced and detailed exploration of the ways in which TIW has been applied to guide research design or interpret data, how it has been developed or expanded, and how it is discussed in terms of rationales for use as well as strengths and weaknesses. The research questions for this study are:
RQ1: In research using the TIW, how is it applied?
1-1 How does TIW inform research design?
1-2 Is TIW applied in part or as a whole?
1-3 What other concepts or theories are used alongside TIW?
RQ2: In research that generates or develops TIW, in what ways is TIW revised, expanded upon, or used to inform other models or theories?
2-1 What revisions or expansions to TIW are proposed?
2-2 What alternative formulations of TIW are proposed?
2-3 What new concepts, models, or frameworks are informed by TIW?
RQ3: In research that applies, develops, or substantially discusses TIW, how are its implications and applications considered?
3-1 What strengths of TIW are reported?
3-2 What weaknesses of TIW are reported?
This exploratory and descriptive study reports on the status of TIW’s empirical application and theoretical development, and offers recommendations for continued application and development of TIW in future in light of the findings. This study aims to contribute to ongoing conversations about theory use and development in LIS by offering an in-depth examination of how TIW has been applied, interpreted, and adapted in LIS scholarship. This study may build awareness of a relatively newer, lesser known theory native to LIS and address concerns about the potential dearth or decline of theory in LIS.
2. BRIEF LITERATURE REVIEW
2.1. Theory Use in LIS
The concept of “theory” can be defined differently depending on the academic context and purpose. Buckland (1991) viewed theory as a framework for explaining or expanding the essence of phenomena, whereas Popper regarded theory as a set of laws that can be empirically tested. A model, which is often used interchangeably with theory, is defined as a framework for analyzing problems and describing relationships (Wilson, 1999). However, it is distinct from a theory. Frankfort-Nachmias and Nachmias (1996) specify the difference in that a theory explains phenomena and a model describes phenomena. Therefore, the use of theory as a tool for analyzing and explaining phenomena, rather than merely describing them, can serve as a measure of research maturity and reliability (Brookes, 1980; Houser, 1988; Van Maanen, 1998).
The field of LIS has advanced through the development, application, and expansion of its own theories. LIS theories enable deeper understanding of human information behaviors, provide critical insights for the design of effective information systems, improve library collections and services, and inform the education and training of librarians and other information professionals. Since the 1990s and early 2000s, the use and application of theories in LIS research have increased (Kim & Jeong, 2006). However, Kim and Jeong (2006) note that despite this increase, articles specifically focused on developing theory were trending down. A decline in theory use has been noted by other researchers as well. Julien et al. (2011) noted decreasing theory use in information behavior research articles published between 1999 and 2008. Vakkari (2008) and VanScoy et al. (2022) identified overall decreases in theory use in LIS conference papers. Additionally, researchers have identified the trend of importing theories from neighboring disciplines, such as sociology, psychology, and business, for use in LIS (Pettigrew & McKechnie, 2001; Ukwoma & Ngulube, 2021; VanScoy et al., 2022). Interdisciplinary approaches may enhance the diversity and depth of LIS research, create new research opportunities, and speak to the meta-disciplinarity of information and information behaviors. However, these trends have spawned some existential dread among LIS scholars about the identity and theoretical foundations of the discipline.
Vakkari et al. (2022) looked at articles published in connection with authors’ disciplines and found that LIS articles published by LIS scholars accounted for about one-third of the publications. They noted significant contributions from computer science, business, economics, the humanities, the natural sciences, and medicine. Vakkari et al. (2022) argue that their findings support previous arguments from Nolin and Åström (2010) that LIS is a fragmented adhocracy (Whitley, 1984), meaning that LIS is a field in which there is inconsistency or disagreement on research areas and methods and less dependence of scholars upon one another in building knowledge. Bates (2009) and Raber (2003) describe a variety of different definitions, theories, and paradigms within the discipline but note that LIS continues to progress.
Studies have been conducted to examine the extent to which theories are utilized in LIS research. Lund (2019) found that Kuhlthau (1991)’s information search process (ISP) and Bates (1989)’s berrypicking are by far the most frequently cited theories in LIS. However, the sample of theories used by Lund (2019) was determined by those included in Fisher et al. (2005)’s textbook, Theories of Information Behavior, which does not include TIW because it had not yet been published. Citation data in the previous study (Park et al., 2022) found that TIW was cited 68 times over 13 years and 9 months (between June 2008, when it was first introduced, to March 2022, the end of data collection), which is roughly 4.95 citations per year, suggesting low awareness or adoption of TIW. Regionally, theoretical applications in LIS studies have been investigated in countries outside the West, such as Korea (Jeong & Kim, 2005), Taiwan (Wu et al., 2017), Tanzania (Kassim, 2024), and Nigeria and South Africa (Ukwoma & Ngulube, 2021). Jeong and Kim (2005) noted that about 10% of studies published in Korean LIS journals apply theories. In Taiwanese LIS journals published between 2010 and 2015, Wu et al. (2017) found that 49.9% of articles applied theory. Ukwoma and Ngulube (2021) found that most studies from LIS postgraduate students and researchers in Nigeria and South Africa used theories from outside disciplines, primarily in management, psychology, and sociology.
The depth or level of theory application has also been explored. Notably, Kumasi et al. (2013) categorized theory talk levels into seven stages: theory dropping, theory positioning, theory diversification, theory conversation, theory application, theory testing, and theory generation. VanScoy et al. (2022) adapted Kumasi et al. (2013)’s theory talk framework to explore the use of theory in ISIC conference papers published between 1996 and 2020. They found that most (around 78%) of the conference papers mention theory, with about 69% percent of papers using theory at a substantial level. VanScoy et al. (2022) also found that most of the theories used originated from LIS, though some from other disciplines, such as sociology, psychology, communication, and business or management, were noted. Similar to Lund (2019), VanScoy et al. (2022) found that Kuhlthau’s ISP was the most used LIS theory. Lund (2021) identified the prominence of ISP in dissertations as well.
Kassim (2024) also applied Kumasi et al. (2013)’s theory talk model in an exploration of theory use in articles published in Tanzanian LIS journals from 1990 to 2023. Kassim also identified an upward trend of theory use after 2006, but only 154 out of 616 (25%) of Tanzanian LIS articles overall included theory. Kassim (2024) also found that 109 (70.3%) applied theory, 29 (18.7%) dropped theories, and 17 (10.9%) generated theory. Contrary to other studies, Kassim (2024) found that the technology acceptance model (TAM; Davis, 1987) and the unified theory of acceptance and use of technology (UTAUT; Venkatesh et al., 2003) were the most often used theories at 17.4% and 14.1%, respectively.
VanScoy et al. (2022) note that while Kumasi et al. (2013)’s theory talk framework was useful for providing terminology and framing the discussion of their findings, there were a variety of limitations. In particular, they describe difficulties in applying the framework to analyze or categorize studies that may not clearly articulate why or how a theory is used, or studies that may not clearly fall into one category. They argue that more development of the theory talk model could make it useful for analyzing the use of theory. In another study applying Kumasi et al. (2013)’s theory talk framework, Park et al. (2022) also note that the framework poses challenges in identifying the usage of specific theories because it considers all theories used in a study. Park et al. (2022) adapted and revised the original framework into the single theory talk framework by applying mutual exclusivity between certain categories and repositioning and redefining the seven original levels into five levels (theory dropping, theory positioning, theory conversation, theory application, and theory generation) to analyze the application of the TIW. Park et al. (2022) found that in the context of articles featuring TIW (n=68), 51.47% were briefly name-dropping TIW; 17.65% were using TIW to position their own study or theory; 4.41% conversed on TIW; 26.47% applied TIW for study design or data analysis or interpretation; and 16.18% used TIW in some way to generate theory. This study will explore the use and application of TIW in greater detail.
2.2. Theory of Information Worlds
The TIW is a framework for analyzing the social aspects of human information behavior. The theory is based on Chatman (1999)’s small worlds theory and Habermas (1992)’s concepts of the lifeworld. Normative information behaviors within Chatman’s small worlds are shaped by social norms, social types, and worldview. Burnett and Jaeger (2008; Jaeger & Burnett, 2010) modified the worldview concept into information value to account for variations in information value systems across worlds because different worlds may evaluate information differently. Additionally, the concept of boundaries was added to account for potential social interaction and exchange of information across worlds, in consideration of Habermas’s concept of the lifeworld. These revisions allow TIW to provide a more holistic perspective on the broader social and cultural contexts of information behavior in a way that small worlds cannot. To study information behavior in social contexts, the TIW (Jaeger & Burnett, 2010, p. 8) presents five key core concepts, defined as follows:
3. METHOD
This follow-up study extends the analysis of a systematic literature review conducted by the authors (Park et al., 2022) to explore research and publication trends of peer-reviewed studies citing or applying Burnett and Jaeger (2008)’s and Jaeger and Burnett (2010)’s TIW. The focus on peer-reviewed research literature proceeded under the assumption that said literature completed higher-level, more competitive and thorough peer review processes; though, of course, this may vary across publication venues. Previous work by Park (2022) focused on TIW use in doctoral dissertations, and so Park et al. (2022) and this study opted to explore the use of TIW in peer-reviewed research articles.
This study builds on the previous by conducting a qualitative content analysis of studies featured in peer-reviewed research articles that have applied or used the TIW at higher levels, such as for theoretical conversation (coded as TC); data collection, analysis, or interpretation (coded as TA); or to inform the development of other concepts or theories (coded as TG). Through a systematic literature review approach informed by Kumasi et al. (2013), Lund (2021), and Williams et al. (2015), Park et al. (2022) identified a sub-sample of 26 peer-reviewed research articles published between 2008, the year the TIW was introduced by Burnett and Jaeger, and 2022 that used the theory at higher levels. Research articles considered for inclusion must have been peer-reviewed, published in English or Korean, and available in full-text via online websites, institutional repositories, author websites, and academic databases accessible to the researchers through their respective institutional libraries.1 Given the research team’s language proficiencies, the sample included articles published in English or Korean. Sampled articles must have cited at least one of the theory’s core works: Burnett and Jaeger (2008; 2011) or Jaeger and Burnett (2010).
The core sample of 26 previously identified articles was expanded using the same systematic literature review approach to include relevant articles published through the end of 2023, which yielded 23 potential new titles given the original selection criteria, as mentioned above. However, after applying the revised single theory talk model, as discussed below, the new TC, TA, and TG additions were narrowed to three titles, and two of the previously collected articles from the original subsample were removed as they no longer met the qualifications to be coded as TG papers. Upon further review during revisions to the single theory talk model, two papers (Oh & Butler, 2019; Riley et al., 2022) previously coded as TP/TG were recategorized as TP only and thus removed from the sample of this study, as while they did identify TIW, it was for positioning (TP) and not for generating new theory (TG). As such, the sample for this study includes 27 articles (n=27).
The previous study (Park et al., 2022) categorized and coded articles using theory at higher levels with a single theory talk model that was adapted from the theory talk framework by Kumasi et al. (2013). During initial codebook development conversations for this study, the single theory talk model was found to need revision and expansion to guide qualitative content analysis and provide additional depth to account for the different ways theory can be used at higher levels. The single theory talk model, as noted in Table 1, was revised primarily to expand the Theory Application (TA) and Theory Generation (TG) codes from the previous study to provide great specificity to account for the different ways theory can be applied, developed, or used to generate new theoretical constructs. The higher-level code of Theory Conversation (TC) and the lower levels of use (0, TD, and TP) were left unchanged.
Table 1
Revised single theory talk model
| Category | Code | Adapted operational definition | Notes |
|---|---|---|---|
| Not Applicable | 0 | Not Applicable (0) is applied when the manuscript does not directly identify or address TIW or its core concepts, even if the core TIW publications are cited. This is used as an exclusionary criterion for screening purposes | Unchanged |
| Theory Dropping | TD | Theory Dropping (TD) is the mention of TIW or its core concepts within the manuscript (with accompanying citations to core TIW publications) but without a clear connection to the main focus of the article, research design, or analysis | Unchanged |
| Theory Positioning | TP | Theory Positioning (TP) is the short discussion, description, or critique of TIW or its core concepts alongside or in relation to other theories used to provide context for the study/manuscript at hand but not as a main focus of the manuscript, nor to guide the research design or analysis. This may include using TIW or core concepts to discuss the findings/results | Unchanged |
| Theory Conversation | TC | Theory Conversation (TC) refers to a focused, in-depth discussion or critique of TIW, its core concepts, or its theoretical implications or practical applications within LIS or in other fields. This category is limited to articles that specifically discuss TIW or its core concepts as part of the core focus of the paper but do not report empirical research using the theory. This may occur in the literature review, discussion, or conclusion sections | Unchanged |
| Theory Application | TA | Theory Application (TA) refers to the application of TIW or its core concepts to the research design or methodology (research questions, design, or method); the analysis or interpretation of empirical data; or the evaluation, assessment, testing, or validation of TIW or its core concepts | Split into TA-1 & 2 |
| Theory Application 1 - Research Design & Data Analysis | TA1 | Theory Application 1 (TA-1) refers to the application of TIW or its core concepts to the research design or methodology (research questions, design, or method), or for the analysis or interpretation of empirical data | |
| Theory Application 2 - Theory Convergence | TA2 | Theory Application 2 (TA-2) refers to the use of TIW or its core concepts alongside other theories or theoretical concepts for the analysis or interpretation of data | Automatically includes TA-1 |
| Theory Generation | TG | Theory Generation (TG) refers to the theoretical development, revision, or expansion of TIW or its core concepts through empirical research or inductive reasoning. This may entail the expansion or revision of TIW, the proposal of propositions, or the building or creation of new theories | Split into TG-1, 2, 3, & 4. |
| Theory Generation 1 - Refinement/Revision | TG1 | Theory Generation 1 (TG-1) - Refinement refers to a proposed refinement or revision to one or more of the existing 5 core concepts of TIW | May overlap with TC |
| Theory Generation 2 - Expansion | TG2 | Theory Generation 2 (TG-2) - Expansion refers to the proposed addition of one or more new concepts alongside the original 5 core concepts of TIW | New concepts may be derived from the existing theory. May overlap with TC, TA-2 |
| Theory Generation 3 - Alternative | TG3 | Theory Generation 3 (TG-3) - Alternative refers to the proposal of an alternative information worlds theory or another similarly scoped theory | May overlap with TC |
| Theory Generation 4 - Informed | TG4 | Theory Generation 4 (TG-4) - Informed refers to new or emergent concepts, models, or frameworks developed through the application or use of TIW to explain or interpret a phenomenon, but not intended as replacements or alternatives to TIW | May overlap with TP, TC, TA-1, TA-2, and other TG categories |
In this study, the revised TA code was split into two subcategories: Theory Application 1 - Research Design & Data Analysis (TA1), which refers to the use of TIW for research design or data analysis; and Theory Application 2 - Theory Convergence (TA2), which refers the use of TIW alongside other theories for the analysis or interpretation of data. Additionally, the revised TG was split into four subcategories: Theory Generation 1 - Refinement/Revision (TG1), when revisions or refinements to TIW are introduced; Theory Generation 2 - Expansion (TG2), when new concepts beyond the original five core concepts are introduced; Theory Generation 3 - Alternative (TG3), when alternative information worlds theories are proposed; and Theory Generation 4 - Informed (TG4), when TIW is used to inform the development of new or emergent concepts, models, or theories that are not alternatives to TIW. The TG1 and TG2 codes are meant to capture the theoretical development of TIW itself through revision or expansion. TG3 and TG4 are meant to capture how TIW may inspire, inform, or build other concepts, models, or theories. The TG3 code is meant to identify theories proposed as alternatives or replacements for Burnett and Jaeger’s TIW, and the TG4 code captures concepts, models, frameworks, or theories that are informed by TIW but are not intended as alternatives or replacements. As noted in Table 1, the codes are not mutually exclusive. Furthermore, while the research team considers the continued application of the theory across disparate research contexts, use with different methods, and use alongside other theories as ways to indirectly contribute to theory development as forms of theory testing, application of the theory does not always imply or guarantee theory development or generation. As seen in Table 2 (Bao & Ke, 2023; Brattland, 2017; Burnett, 2015; Burnett et al., 2009; Burnett et al., 2013; Froggatt, 2015; Gibson, 2016; Gibson & Kaplan, 2017; Hollister, 2020; Hollister et al., 2023; Hovious, 2018; Jaeger et al., 2014; Känsäkoski & Huotari, 2016; Lee, 2019; Lee & Butler, 2019; Ndumbaro & Ochieng, 2021; Ndumu, 2019; 2020; Pang et al., 2020; Park, 2022; Park et al., 2022; Rohman & Pitaloka, 2025; Welch, 2019; Worrall, 2019; Worrall et al., 2021; Xie et al., 2021; Yu, 2012) below, coding an article with TA does not always mean it was also coded with TG.
Table 2
Higher TIW theory use articles coding results
| Sampled articles’ authors & titles (n=27) | Coding |
|---|---|
| Bao, X., & Ke, P. (2023). Chaos, expansion, and contraction: The information worlds of depression patients during the COVID-19 pandemic lockdown. | TA2 |
| Brattland, K. (2017). Information preferences of Reddit communities surrounding the Brock Turner case. | TA2 |
| Burnett, G. (2015). Information worlds and interpretive practices: Toward an integration of domains. | TC, TG2 |
| Burnett, G., Whetstone, M., & Jaeger, P. T. (2013). Personal health record interfaces: A hermeneutic analysis. | TA1 |
| Burnett, K., Subramaniam, M. M., & Gibson, A. (2009). Latinas cross the IT border: Understanding gender as a boundary object between information worlds. | TA2 |
| Froggatt, D. L. (2015). The informationally underserved: Not always diverse, but always a social justice advocacy model. | TA2, TG4 |
| Gibson, A. N. (2016). Building a progressive-situational model of post-diagnosis information seeking for parents of individuals with Down syndrome. | TA2, TG4 |
| Gibson, A. N., & Kaplan, S. (2017). Place, community and information behavior: Spatially oriented information seeking zones and information source preferences. | TA2, TG4 |
| Hollister, J. M. (2020). The information worlds of online role-players. | TA1 |
| Hollister, J. M., Burnett, G., Lee, J., & Skinner, J. (2023). Collaborative codebook development across information worlds: Intersections between pedagogy, theory, and method in three dissertations. | TC |
| Hovious, A. (2018). Toward a socio-contextual understanding of transliteracy. | TG4 |
| Jaeger, P. T., Gorham, U., Bertot, J. C., Taylor, N. G., Larson, E., Lincoln, R., Lazar, J., & Wentz, B. (2014). Connecting government, libraries and communities: Information behavior theory and information intermediaries in the design of LibEGov.org. | TA2, TG2 |
| Känsäkoski, H., & Huotari, M. L. (2016). Applying the theory of information worlds within a health care practise in Finland. | TA1 |
| Lee, J. (2019). An exploratory study on the political information behaviors of Korean opinion leaders on Twitter: Through the lens of theory of information worlds. | TA1 |
| Lee, M., & Butler, B. S. (2019). How are information deserts created? A theory of local information landscapes. | TP, TG4 |
| Ndumbaro, F., & Ochieng, L. M. (2021). Access to information on family planning (FP) methods among married women of reproductive age in Ilala District, Dar es Salaam Tanzania. | TA1 |
| Ndumu, A. (2019). Linkages between information overload and acculturative stress: The case of Black diasporic immigrants in the US. | TA2 |
| Ndumu, A. (2020). Toward a new understanding of immigrant information behavior: A survey study on information access and information overload among US Black diasporic immigrants. | TA1 |
| Pang, N., Karanasios, S., & Anwar, M. (2020). Exploring the information worlds of older persons during disasters. | TA2 |
| Park, S. (2022). A reflection on social perspective of information behavior: Around the theory of information worlds. | TC |
| Park, S. Lee, J., & Hollister, J. M. (2022). A systematic review on the application of the theory of information worlds. | TC |
| Rohman, A., & Pitaloka, D. (2025). Disconnected and disabled during the pandemic: Toward more inclusive pandemic response plans in the Global South. | TA1 |
| Welch, C. (2019). Circling the reality of public institutions: An e-Delphi study of information, culture, and community stakeholders voicing the way forward in Detroit, Michigan. | TA2 |
| Worrall, A. (2019). “Connections above and beyond”: Information, translation, and community boundaries in LibraryThing and Goodreads. | TA2 |
| Worrall, A, Cappello, A, & Osolen, R. (2021). The importance of socio-emotional considerations in online communities, social informatics, and information science. | TA1, TG4 |
| Xie, J., He, Z., Burnett, G., & Cheng, Y. (2021). How do mothers exchange parenting-related information in online communities? A meta-synthesis. | TA1 |
| Yu, L. (2012). Towards a reconceptualization of the ‘information worlds of individuals.’ | TP, TG3 |
The revised single theory talk model provided the framework for directed content analysis to categorize and analyze the sampled articles (Hsieh & Shannon, 2005). Additional qualitative content analysis was conducted using open coding to identify content relevant to the research questions and any related emergent themes.
Intercoder reliability testing and consensus building were used to ensure the consistency and trustworthiness of the codebook and data analysis. A collaborative approach similar to Cascio et al. (2019) was used to establish intercoder consensus with each of the authors of this study serving as coders. During codebook development, each article was assigned two coders in a sequence that allowed the coders to be evenly distributed across the sample, resulting in each author coding two-thirds of the sample. Coding during initial codebook development was done in batches of 3-5 articles, followed by a meeting to discuss the coding as a whole research team and adjust the codebook as needed. Given the small size and nature of the sample (n=27), the entire research team applied the final codebook to each of the articles, yielding an intercoder reliability rating of 92.59%, which is well above an acceptable level of agreement (80%) as argued by Lombard et al. (2002). Open coding and the resulting emergent themes identified during additional content analysis, as guided by research questions, were vetted through cumulative discussion and consensus-building. Additional intercoder reliability testing was conducted to explore whether TIW is applied fully (91.67% intercoder reliability rating, n=20) in TA-coded articles, as well as whether the core concepts are present in the results/findings or discussion sections of the TA-coded articles (89.167% agreement, n=20).
This study is limited in scope by focusing on peer-reviewed research articles published between 2008 and 2023, and is limited by the availability of full-text access and library database subscriptions. The limitations in scope, sampling, and the use of qualitative methods mean the findings are not generalizable or predictive. However, the trends and themes identified may also exist in types of research materials employing TIW, such as conference papers, dissertations, or research articles not included in the sample of this study. Additionally, the systematic literature review approach, intercoder reliability testing, and consensus building enhance the dependability and confirmability of the findings.
To ensure transparency and credibility, it should be noted that all members of the research team have previous work related to TIW. Hollister (2020) and Lee (2019) have applied TIW in empirical research and worked with Burnett in a TIW-focused theory study group (Hollister et al., 2023), all of which are included in the sample of this paper. As noted in the introduction and literature review, previous studies led by Park (2022) (Park et al., 2022) have explored the use of TIW, and this study extends those explorations. The core analysis of this paper is structured around the revised single theory talk model, not TIW. As noted in Section 2.1, Kumasi et al. (2013)’s theory talk framework and adaptations thereof have been applied in other explorations of theory use in the research literature. The dependability of the qualitative analysis is supported by a robust approach to inter-coder reliability testing and consensus building, which used the entire sample rather than a subsample and yielded high levels of agreement (O’Leary, 2005; Pickard & Childs, 2013). To further enhance trustworthiness and confirmability and to avoid or mitigate potential interpretive bias, the findings and interpretations thereof are supported with evidence from the data (Pickard & Childs, 2013).
4. FINDINGS
4.1. Applications of TIW (RQ1)
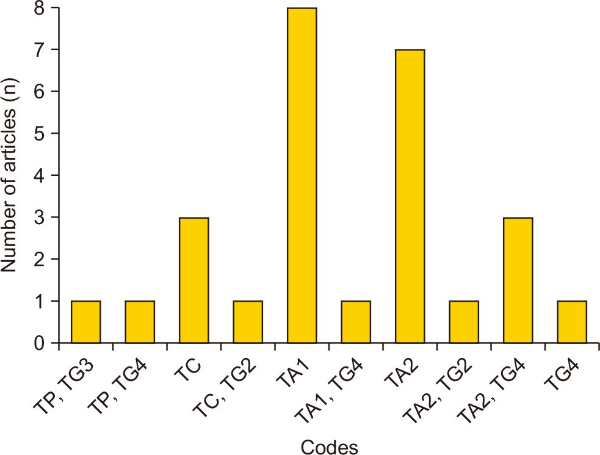
This study analyzed 27 papers that applied the TIW. The codes used in TA papers, which applied the theory, and TG papers, which provided new theoretical concepts, are TP, TC, TA1, TA2, TG2, TG3, and TG4. Although TP papers, which use TIW to position a study without applying it to research design or data analysis, were not the subjects of analysis, the corresponding codes were included in this study’s analysis when used alongside other TC, TA, or TG codes. A total of 35 codes were assigned across the 27 papers, with an average of approximately 1.3 codes per paper. The most frequently assigned codes were TA1 and TA2, which appeared in 10 papers each. Following those were TG4, which appeared six times, TC four times, TG2 and TC two times each, and TG3 one time. Abbreviated citations of the articles and their associated codes are listed in Table 2 (Bao & Ke, 2023; Brattland, 2017; Burnett, 2015; Burnett et al., 2009; Burnett et al., 2013; Froggatt, 2015; Gibson, 2016; Gibson & Kaplan, 2017; Hollister, 2020; Hollister et al., 2023; Hovious, 2018; Jaeger et al., 2014; Känsäkoski & Huotari, 2016; Lee, 2019; Lee & Butler, 2019; Ndumbaro & Ochieng, 2021; Ndumu, 2019; 2020; Pang et al., 2020; Park, 2022; Park et al., 2022; Rohman & Pitaloka, 2025; Welch, 2019; Worrall, 2019; Worrall et al., 2021; Xie et al., 2021; Yu, 2012).
Since a paper can have multiple codes, the study analyzed papers that applied the theory through combinations of codes. When considering combinations of codes, 10 code combinations were used, and the number of papers per combination is shown in Fig. 1. The code that appeared in most papers was TA1 (in eight papers). This was followed by TA2 in seven papers, and TC and TG4 in three papers each.
Fig. 1
The number of articles per unique code. Please see Section 3 or Table 1 for more information. TP, Theory Positioning; TC, Theory Conversation; TA1, Theory Application 1 - Research Design & Data Analysis; TA2, Theory Application 2 - Theory Convergence; TG2, Theory Generation 2 - Expansion; TG3, Theory Generation 3 - Alternative; TG4, Theory Generation 4 - Informed.
4.1.1. RQ1-1: TIW-Informed Research Designs
In the research design process, TIW was utilized for grounded theory data collection guidance (Gibson, 2016), the development of survey instruments (Froggatt, 2015), and the design of interviews and their protocols (Froggatt, 2015; Gibson & Kaplan, 2017). Although the analysis was constrained by the limited space available in academic journal articles, which restricts access to detailed survey or interview questions, the analysis techniques addressed key concepts of TIW. Additionally, the authors of those works explicitly mentioned the use of TIW in creating their research instruments, confirming its application in the research design phase.
4.1.2. RQ1-2: The Application of TIW Core Concepts
To investigate how the TIW was applied in the sampled papers, the analysis was divided into two sections: research design and research results. The research design provides the overall framework for conducting the study, including the literature review and methodology. The literature reviews of the sampled papers were examined to determine whether TIW and its five key concepts were explained, and the methodology sections of the sample papers were assessed as to whether TIW was used during the development of research instruments. The analysis revealed that most studies, except one, referred to TIW and its key concepts at the research design stage. Among the 20 analyzed papers, 12 studies (60%) established their research questions based on TIW. Notably, Känsäkoski and Huotari (2016) formulated the following research question: “Which concepts of the theory by Burnett and Jaeger can be identified as elements of the organizational culture that enhance or inhibit the value creation of the ICP?” This serves as a direct example of TIW being used in research question development. Furthermore, Burnett et al. (2009) employed TIW to explore how successful Latina IT professionals construct and reconstruct their conceptions of gender before, during, and after engaging with the information world of the IT industry.
To illustrate how the five core concepts of the TIW were applied across the selected studies, we present representative excerpts from the analyzed literature. These excerpts demonstrate how each concept—social norms, social types, information behavior, information value, and boundaries—was interpreted and operationalized within different research contexts.
Social norms were often reflected in community expectations and implicit behavioral codes. In Xie et al. (2021), mothers participating in online parenting communities “generally achieved a sense of what is and is not ‘normal’ through reading about others’ experiences” (pp. 5-6). This finding illustrates how shared narratives and interactions contribute to constructing social norms that shape acceptable information practices within a particular information world.
Social types were used to classify individuals according to their perceived roles and patterns of engagement in information environments. In Bao and Ke (2023), participants were observed to “play multiple information roles and ‘social types’; they are information demanders, receivers, and providers” (p. 982). This conceptualization of role-based identities influenced how information was circulated, negotiated, or restricted within the group.
Information behavior, as expected, appeared most frequently across the studies and encompassed practices of seeking, avoiding, or sharing information. Ndumu (2019) emphasizes that “stress, anxiety, and feelings are vital considerations when analyzing immigrants’ engagement with information” (p. 4), underscoring the importance of affective dimensions in shaping individual information practices.
Information value was discussed in relation to the criteria individuals use to assess the relevance, credibility, or ideological alignment of information. For example, in Welch (2019), among the top five issues listed by both community advocates and library, archives, and museum (LAM) practitioners was “Foundations exhibit White supremacist values that frame communities as needing to be saved or be complacent” (p. 254). This observation highlights how deficit-oriented narratives were perceived to be devalued by foundations, while critical, anti-racist, and community-empowering knowledge was regarded as more meaningful to both community advocates and LAM practitioners. Welch (2019) provides examples of how information values can be shared or differ across and between stakeholders, community groups, and organizations within interrelated or overlapping information worlds.
Boundaries, defined as conceptual or structural limits to participation or access, consistently emerged as a salient factor, particularly among marginalized groups. In their study on disaster information access, Pang et al. (2020) found that older adults “did not report using social media, the Internet, or mobile applications,” a finding the authors attribute to the “age and socioeconomic profile of the subjects” (p. 628). This demonstrates how demographic and technological divides can function as barriers to information engagement in urgent contexts.
Together, these excerpts offer a glimpse into the diversity of ways TIW concepts are interpreted and embedded in empirical work, reinforcing the theory’s adaptability across domains and populations.
The results of examining the usage of the five concepts from the TIW in the results and discussion sections are shown in Table 3. The concept most frequently discussed in the results is “information behavior,” appearing in 16 TA papers (80%). This seems to be because the TIW was designed to analyze people’s information behavior, leading to the frequent use and analysis of the concept of information behavior. Next, the concept of “information value” appeared in the results of 15 papers, accounting for 75% of all TA papers. The least frequently mentioned concept was “social types,” which appeared in the results section of seven papers, or 35% of the total papers.
Table 3
Use of TIW core concepts in findings and discussion sections (n=20)
| Social norms | Social types | Information value | Information behavior | Boundaries | |
|---|---|---|---|---|---|
| Findings | 11 (55) | 7 (35) | 15 (75) | 16 (80) | 11 (55) |
| Discussion | 15 (75) | 12 (60) | 16 (80) | 17 (85) | 15 (75) |
In the discussion sections of the sampled articles, the most frequently mentioned concept was also “information behavior,” followed by “information value,” which appeared in 80% of the papers. Similar to the trends in the results section, the concept of “social types” appeared in the discussion section of 12 papers, but it was still the least frequently mentioned among the five concepts.
4.1.3. RQ1-3: Complementary Concepts or Theories
TIW has been used in conjunction with other theoretical frameworks or concepts in scholarly literature. Table 3 summarizes the frequencies of complementary theories and concepts that appeared alongside TIW in the 27 articles analyzed. This analysis addresses Research Questions 1-3 (RQ1-3), which seek to identify what other theories or concepts are used alongside TIW and to what extent TIW operates independently as a theoretical framework.
Table 4 (Bowker & Star, 1999; Brattland, 2017; Burnett et al., 2009; Charmaz, 2014; Corbin & Strauss, 2008; Currie & Suhomlinova, 2006; Dunne, 2002; Elder et al., 2003; Engeström, 1987; Froggatt, 2014; 2015; Gibson, 2016; Gibson & Kaplan, 2017; Harding, 2015; Hovious, 2018; Huotari & Chatman, 2001; Jaeger et al., 2014; Jones, 1997; Känsäkoski, 2014; Känsäkoski & Huotari, 2016; Kuhlthau, 1991; Ndumu, 2019; 2020; Pang et al., 2020; Rudmin, 2009; Ruthven, 2022; Savolainen, 2008; Sonnenwald, 1999; Star, 1989; Star & Griesemer, 1989; Strauss, 1987; Welch, 2019; Wenger, 1998; Worrall, 2019) presents 19 distinct theories and concepts that were used in combination with TIW across the sample. The category with the highest frequency in Table 4 (Bowker & Star, 1999; Brattland, 2017; Burnett et al., 2009; Charmaz, 2014; Corbin & Strauss, 2008; Currie & Suhomlinova, 2006; Dunne, 2002; Elder et al., 2003; Engeström, 1987; Froggatt, 2014; 2015; Gibson, 2016; Gibson & Kaplan, 2017; Harding, 2015; Hovious, 2018; Huotari & Chatman, 2001; Jaeger et al., 2014; Jones, 1997; Känsäkoski, 2014; Känsäkoski & Huotari, 2016; Kuhlthau, 1991; Ndumu, 2019; 2020; Pang et al., 2020; Rudmin, 2009; Ruthven, 2022; Savolainen, 2008; Sonnenwald, 1999; Star, 1989; Star & Griesemer, 1989; Strauss, 1987; Welch, 2019; Wenger, 1998; Worrall, 2019) is “None” (seven occurrences), indicating that many studies used TIW as a standalone theory. This suggests that TIW can function effectively as an independent theoretical framework. Acculturative stress (Rudmin, 2009), activity theory (Engeström, 1987), social world perspective, boundary objects, and translation (Bowker & Star, 1999; Star, 1989; Star & Griesemer, 1989; Strauss, 1987), grounded theory (Charmaz, 2014; Corbin & Strauss, 2008), and information overload (Bawden & Robinson, 2009; 2013) each appear twice, making them the most commonly used complementary theories alongside TIW in the sample. Notably, acculturative stress and information overload were repeatedly used in two papers by the same author on similar research projects, and activity theory and boundary objects were applied in two separate papers by different authors.
Table 4
Frequency of complementary concepts or theories
| # of papers mentioning (TA2, n=10) | Concepts or theories and primary cited sources | As cited in |
|---|---|---|
| 7 | None | Not applicable |
| 2 | Acculturative stress (Rudmin, 2009) | Ndumu (2019; 2020) |
| Activity theory (Engeström, 1987) | ||
| Social worlds perspective/boundary objects/translation (Bowker & Star, 1999; Star, 1989; Star & Griesemer, 1989; Strauss, 1987) | ||
| Grounded theory (Charmaz, 2014; Corbin & Strauss, 2008) | ||
| Information overload (Bawden & Robinson, 2009; 2013) | Ndumu (2019; 2020) | |
| 1 | Bridges (Jaeger et al., 2014) | Jaeger et al. (2014) |
| Everyday life information seeking (Huotari & Chatman, 2001) | Känsäkoski & Huotari (2016) | |
| Communities of practice (Wenger, 1998) | Brattland (2017) | |
| Dynamic structural model of racism (Jones, 1997) | Welch (2019) | |
| Everyday information practice (Savolainen, 2008) | Froggatt (2015) | |
| Information horizon theory (Sonnenwald, 1999) | Gibson & Kaplan (2017) | |
| Information search process (Kuhlthau, 1991) | Froggatt (2015) | |
| Life course theory (Elder et al., 2003) | Gibson (2016) | |
| Organisational culture (Currie & Suhomlinova, 2006) | Känsäkoski & Huotari (2016) | |
| Value creation (Huotari & Chatman, 2001; Känsäkoski, 2014) | Känsäkoski & Huotari (2016) | |
| Persons-in-progressive-situations (Dunne, 2002) | Gibson (2016) | |
| Rape culture (Harding, 2015) | Brattland (2017) | |
| Theory of informationally underserved (Froggatt, 2014) | Froggatt (2015) | |
| Transition (Ruthven, 2022) | Bao & Ke (2023) |
In addition, 14 concepts or theories appeared only once alongside TIW. In the field of library and information science, theories such as Kuhlthau (1991)’s ISP, Chatman’s Everyday Life Information Seeking (Huotari & Chatman, 2001), and Information Horizon Theory (Sonnenwald, 1999) were used in conjunction with TIW. There were also cases where new concepts, rather than established theories or models, were introduced. For instance, Jaeger et al. (2014) incorporated the concept of bridges to conduct their analysis. Froggatt (2015)’s study applied TIW alongside Savolainen (2008)’s everyday information practices and Kuhlthau (1991)’s ISP to develop a theory of the informationally underserved (IU), which describes student success and academic achievement in relation to the accessibility or availability of school library programs.
The diverse range of complementary theories reveals the epistemological versatility of TIW. Drawing on TIW, researchers have successfully integrated frameworks that span cognitive (e.g., ISP), affective (e.g., acculturative stress), social-structural (e.g., boundary objects), and methodological paradigms (e.g., grounded theory). The analysis of concepts or theories used with TIW demonstrates that TIW is a robust tool for analyzing information phenomena on its own. Moreover, it indicates that when combined with other tools, TIW serves as a useful framework for addressing research questions in diverse contexts.
4.2. Theory Revision, Expansion & Generation with the Theory of Information Worlds (RQ2)
As noted above, nine articles were involved in theory generation using TIW. However, none of the articles propose revisions to the existing core concepts of TIW (TG1, n=0).
4.2.1. RQ2-1: Expansions to TIW (TG2)
Expansions to TIW are proposed in two articles (TG2, n=2): Burnett (2015) and Jaeger et al. (2014). Burnett (2015) proposes an expansion to the TIW by introducing the information domains framework. Two new domains, the domains of the individual and of signification, are added, with the original TIW being repositioned unchanged as the domain of the social. The domain of the individual is meant to capture individual factors, such as cognition, affect/emotion, agency, etc., to account for, in part, limitations raised by Yu (2012), as well as to encompass myriad other theories and research on individual information behaviors, such as Dervin (1992)’s sense-making and Kuhlthau (1991)’s ISP, among others. The domain of signification accounts for the various languages, representations, tools, and technologies through which information is stored and communicated. The domain of signification is influenced by semiotics and hermeneutics and can also account for physical representations of information as addressed in the LIS literature, such as Buckland (1991)’s information-as-thing, among others.
Jaeger et al. (2014) introduce a potential sixth core concept: bridges. Bridges are defined as “the tangible (physical or digital) mechanisms and channels that facilitate the exchange of information and interaction across boundaries” (Jaeger et al., 2014; para. 13). Through an analysis of an e-government website (LibEGov.org) using TIW, they found that the concept of bridges could characterize the roles in supporting librarians to use and provide e-government services and resources in their libraries, communicate with government agencies, and establish and follow best practices. Bridges may also help describe how information moves across or between information worlds, across boundaries.
4.2.2. RQ2-2: Alternative Formulations of TIW (TG3)
Alternative formulations of TIW are presented in one article (TG3, n=1): Yu (2012). As noted in the literature review, Yu (2012) introduces a TIW of individuals because they argue that Burnett and Jaeger’s TIW does not explicitly define an individual’s information world nor differentiate one’s individual information world from one’s social worlds (Yu, 2012, p. 4). Yu (2012)’s information worlds of the individuals can be defined as the “space-time-intellect delimited life sphere in which information or knowledge afforded by Popper’s worlds 1, 2, and 3 is converted into personal information assets through intentional, conscious and involuntary information practices that are performed by the individual as an information creator, provider, transmitter, seeker, receiver, and user” (Yu, 2012, p. 15). Yu’s TIW of individuals is informed by Popper’s three worlds: physical, objective knowledge, and mental states (Popper, 1979). Yu argues that the boundaries of the information worlds of individuals are based on an individual’s information practices rather than social norms, in contrast to Chatman (1991)’s information or small worlds.
4.2.3. RQ2-3: New Concepts or Theories Informed by TIW (TG4)
New concepts or theories informed by TIW are identified in six articles (TG4, n=6): Froggatt (2015); Gibson (2016); Gibson and Kaplan (2017); Hovious (2018); Lee and Butler (2019); and Worrall et al. (2021).
In a mixed-methods study, Froggatt (2015) explores the impact of access to active school library programs (ASLP) on students’ academic performance. Froggatt (2015) uses TIW as the basis of a proposed model for the theory of the IU. The IU model proposes four information worlds of students: IW-A, where students have access to ASLP and achieve academic success; IW-B, where students have access to ASLP but have no or low academic success; IW-C, where students do have limited or no access to ASLP and still have academic success; and IW-D, where students have limited or no access to ASLP and have no or low academic success. Froggatt (2015) notes that their study does not adequately address IW-B. Access to public libraries and familial support may account for IW-C, and IW-D correlates with low standardized testing scores. Froggatt (2015) argues that the implications of the IU theory and findings stress the importance of information access and support Rioux (2010)’s calls for integrating social justice meta-theory into LIS scholarship, education, and professional practice.
In interviews with the parents of children with Down syndrome, Gibson (2016) used TIW as one of the sensitizing theories to guide data collection and derived a model of post-diagnosis information-seeking behavior. The model represents a progressive process impacted by cognitive, affective, behavioral, situational, and contextual factors. Further analysis and interpretation were informed in part by TIW by Gibson and Kaplan (2017) on the same interview sample with the addition of social network mapping to create a framework for information access in local communities. The framework seeks to understand how place and social contexts impact information seeking (Gibson & Kaplan, 2017, p. 138). The framework consists of four facets: “1. Spatial information access zones in terms of distance from the information seeker; 2. Information seeking effort (in this case measured by minutes of travel); 3. Preferences for fulfillment of information needs in certain zones; 4. Measuring fulfillment of those preferences or expectations.”
Through a systematic literature review, Hovious (2018, p. 183) combines TIW with activity theory (Engeström, 1987) to redefine transliteracy as the “ability to adapt a literacy practice successfully across activity systems.” Hovious (2018, p. 182) argues that TIW is a “useful framework for understanding literacy within information technology-based contexts.”
Lee and Butler (2019) use TIW to position and propose a theory of local information landscapes. They note that TIW helps to explain how social and contextual factors influence information access and behaviors. However, the theory of local information behavior is not derived from TIW, but rather informed or situated by it. The theory of local information landscapes is presented as a supplement to TIW and related theories rather than as an alternative and focuses more on information provision and its impacts on information behavior and access.
Through a mixed methods study using TIW, Worrall et al. (2021) propose and advocate for a paradigm shift in LIS research towards an integration of the social and affect paradigm, and propose a preliminary and informal model of a socio-emotional information science research paradigm. They argue that social theories and paradigms within information science, presumably TIW included, do not adequately develop or integrate affective factors into social information behavior research.
4.3. Theory Conversations with TIW (RQ3)
TC-coded articles discuss the theoretical implications and practical applications of TIW as well as offer critiques and other considerations, but do not use TIW to inform research design or collect and analyze empirical data. TC-coded articles, as well as those coded with TA and TG, identified and discussed the strengths and weaknesses of TIW. Consequently, the strengths and weaknesses of TIW identified across the sample are discussed in Sections 5.3 and 5.4, respectively, with supporting evidence.
Four articles within the sample are coded for theory conversation (TC): Burnett (2015); Hollister et al. (2023); Park (2022); and Park et al. (2022). Burnett (2015) presents a theory development paper that introduces an expansion of core TIW with the addition of the domains of individual and signification; the original core concepts are repositioned as the domain of the social. The new information domains framework can account for other theoretical paradigms and existing research in LIS, such as cognitive and physical paradigms (using Raber’s 2003 interpretations).
Hollister et al. (2023) describe the development of a TIW general codebook through a collaboration of three (then) doctoral candidates and Burnett. They found that TIW provides a scalable and flexible theory that could be successfully applied with a variety of research methods and in disparate research contexts. Park (2022) and Park et al. (2022) are precursors to the study presented here, exploring the use and applications of TIW in dissertations and peer-reviewed research articles, respectively. Both studies find that while TIW is often employed with qualitative methods, it has and continues to be applied with mixed and quantitative methods and is used to study social information behavior in a variety of populations around the world.
5. DISCUSSION
The findings are first summarized and discussed in order of the primary research questions. Given the nature of the TC code, articles featuring substantial discussion or critique of TIW will be described and discussed. Strengths and weaknesses identified during the full analysis are also discussed.
5.1. Theory Application
TIW has been demonstrated to be a versatile and robust theoretical framework applicable across various research contexts. The findings show that TIW effectively operates as an independent analytical tool, with many studies employing it exclusively to explain information phenomena. This highlights the theory’s self-contained theoretical structure, enabling researchers to leverage its value in specific research settings. TIW’s core concepts, particularly “information behavior” and “information value,” were frequently utilized, underscoring the theory’s optimization for analyzing information behavior. In particular, information value can be considered a unique concept of TIW, as it represents a shift from the world view concept in the process of developing Chatman’s original theory into TIW (Jaeger & Burnett, 2010). In the TC article, Hollister et al. (2023), there are specific examples of how to operationalize and apply the information value concept across three different research projects, which may be useful for those thinking about using the information value concept or TIW more fully. However, concepts such as social types and boundaries have been discussed relatively less frequently, and research on social types appears to be limited due to the difficulty of measuring the perception of assigned roles within society. Therefore, to enhance the extensibility of TIW, it may be necessary to clearly define and operationalize the concept of social types. As noted in Hollister et al. (2023), a draft of the general TIW codebook is available by request, which may help scholars to operationalize and apply the TIW concepts to guide their research and interpret their data.
TIW has also made contributions to research design by guiding the development of research questions, data collection methods, and research instruments. For example, TIW was useful in the creation of interview protocols (Gibson & Kaplan, 2017) and survey tools (Worrall, 2019), demonstrating its practical utility in empirical research. When combined with qualitative research methodologies, such as grounded theory (Gibson, 2016), TIW facilitated systematic analysis of complex social phenomena. Its core concepts were explicitly referenced during study design, ensuring that data collection and interpretation were aligned with the theory’s foundational principles. Methodologically, TIW has been leveraged in diverse research designs, including mobile ethnography (Pang et al., 2020), sentiment analysis (Worrall et al., 2021), and cognitive mapping (Bao & Ke, 2023). These applications illustrate TIW’s adaptability to both qualitative and quantitative methods, reinforcing its role as a versatile analytical framework. However, despite its strengths, challenges remain in quantifying individual cognition and emotions within TIW. Future research should focus on refining operational definitions of social types, integrating quantitative models, and developing theoretical frameworks that incorporate effective computing to enhance TIW’s explanatory power.
TIW has demonstrated strong synergy with various theoretical frameworks, enhancing its applicability across diverse research contexts. It has been integrated with Boundary Object Theory (Worrall, 2019), Information Overload (Ndumu, 2019; 2020), and Grounded Theory (Gibson, 2016; Lee, 2019) to provide deeper insights into information behavior. Additionally, it has been applied alongside activity theory to analyze transliteracy (Hovious, 2018) and the information behaviors of rural seniors during disasters (Pang et al., 2020), and with Social Informatics to examine socio-emotional interactions in online communities (Worrall et al., 2021). These integrations collectively highlight TIW’s flexibility in capturing both structural and affective dimensions of information behavior, demonstrating its ability to adapt to various research paradigms while maintaining theoretical coherence.
5.2. Theory Revision, Expansion & Generation
As seen in Section 4.3, although no modifications to the five core concepts of TIW were identified, TIW itself has seen some development and has been used to inform the development of other concepts, models, and theories. Jaeger et al. (2014)’s introduction of the bridges concept and Burnett (2015)’s own addition of domains are the only substantive theoretical developments of TIW, the latter especially so. Burnett (2015)’s information domains are coded as TC and TG2 as the domains framework absorbs the core TIW into the domain of the social and expands the framework with the introduction of the domains of the individual and signification. As such, the information domains can be seen as an expansion and not a replacement. As seen in the results, TIW is still functional as an independent theory and has continued to be used well after the introduction of the information domains framework. Yu (2012)’s TIW of individuals is positioned as an alternative to TIW, but is based on Popper (1979)’s three worlds rather than Chatman (1999; 2000)’s small worlds; and Yu also admits that research with Burnett and Jaeger’s TIW or other social information theories may still better address social aspects of and societal impacts on information behavior, as noted in Section 5.4.
TIW also informed the development of other theories, concepts, and models as seen in articles coded with TG4. Froggatt (2015) identifies different information worlds through interactions of student academic success and access to school library programs. Gibson (2016) uses TIW as one sensitizing theory to develop a model of post-diagnosis information seeking. Gibson and Kaplan (2017) develop a framework of information access in local communities. Similarly, Lee and Butler (2019) consult TIW to develop a theory of local information landscapes. Hovious (2018) combines TIW with activity theory (Engeström, 1987) to redefine transliteracy. Worrall et al. (2021) argue for a social-affective paradigm shift in LIS research, in part informed by TIW. These findings suggest that TIW is useful for informing the development of other theories.
5.3. Strengths: Research Contexts, Methodological Flexibility & Theoretical Amicability
As seen above and in the previous study (Park et al., 2022), TIW has been applied in a variety of research contexts, methods, and alongside other concepts, models, and theories. The scalability of TIW appears useful for exploring and describing multiple-level sociotechnical contexts, enabling its use across various research populations and phenomena ranging from social media users, medical practitioners, immigrants, online gamers, health information systems, to topics such as information access, digital inclusion, and information behavior (Park et al., 2022). Bao and Ke (2023, p. 974), pointing to Burnett and Jaeger’s 2011 chapter, explain that TIW is useful for understanding the social dimensions of information use as well as it “endows it with meaning through the multilevel context in which it occurs, so as to deepen the understanding the role of social and structural factors in shaping information behavior in society.” Känsäkoski and Huotari (2016, p. 336)’s study was one of the first to apply TIW to a micro-level information world setting of health care professionals and patients, and conclude that TIW “could be applied in wider contexts to increase understanding of the intersection among individuals in small worlds, in the meso worlds in which they work, and in the macro world in which they live.” Gibson and Kaplan (2017, p. 138) note that TIW, among other theories, “acknowledge[s] the social multiplicity inherent in physical information places.” Welch (2019, p. 246) found TIW useful for understanding the “conceptual, social, technological, and political context of [information behavior]” in their mixed-methods study on LAM professionals in Detroit. Lee and Butler (2019) found that TIW is helpful for understanding issues related to information access and information behaviors. Ndumu (2019; 2020) also found that TIW helps both to describe the information behaviors and to contextualize the information overload and acculturative stress experienced by Black immigrants in the US. Park (2022) noted similar strengths identified through dissertation projects using TIW.
Another area of strength is TIW’s methodological flexibility, allowing it to be applied with various research methodologies, whether quantitative, qualitative, or some combination thereof. This is in line with the original intention for TIW to be amethodological (Jaeger & Burnett, 2010). Although TIW was more often used with qualitative methods, as noted in Park (2022) and Park et al. (2022), it has been applied with quantitative methods as well. Froggatt (2015) developed a survey questionnaire regarding students’ information behaviors and information access from their contextual small, meso, and life worlds. Jaeger et al. (2014, para. 10) used surveys, site visits, usability and accessibility testing methods to examine user’s information needs, access, and behaviors “from the micro (the localized small worlds of information), to the meso (the intermediate levels of information in society), to the macro (the largest level of information flow in society)” while using e-government websites and services provided by public libraries. However, it should be noted that quantitative data collection and analysis methods were mostly used as parts of mixed and or multiple methods to triangulate findings from multiple data sources and provide holistic views of phenomena.
The most frequently used research methods among the sampled articles are qualitative, including data collection and analysis approaches, such as interviews, focus groups, content analyses of documents/texts, field diaries, and observation. Gibson (2016) and Gibson and Kaplan (2017)’s work used TIW to develop interview protocols in their grounded theory studies; Gibson (2016, p. 3) reported that “[TIW] is useful for guiding grounded theory data collection as it provides a framework for describing actor, information behaviors, information values, and boundaries within and between information worlds without imposing specific coding categories.” The five core concepts of social types, social norms, information behaviors, information value, and boundaries allow researchers to capture a wide spectrum of normative information behaviors and practices in social worlds, information values influenced by social types and norms, as well as conflicts and dynamics in, out, between, and across the multiple boundaries. TIW can be used as a guiding lens without specifying certain social types, social norms, information behaviors, information values, and boundaries; these are based on the unique data from the persons, communities, and contexts under study.
However, some studies feature a shared codebook to aid data collection and analysis. Hollister (2020) and Lee (2019) used a collaboratively developed codebook to analyze information worlds of Massively Multiplayer Online Role-Playing Game users and political opinion leaders on Twitter from their respective doctoral dissertation projects. Although the codebooks used in Hollister (2020) and Lee (2019) were initially based on inductively chosen codes for five core concepts, new codes were added through collaborative work and discussions with one of the theorists of TIW, Dr. Gary Burnett, and another (then) doctoral student, Julia Skinner, as well as deduced through coding research data across three different dissertation projects, as described in Hollister et al. (2023). Park (2022, p. 438) pointed out that “codebook development process using both inductive and deductive approaches contributed to expanding TIW,” and Hollister et al. (2023) maintain that collaborative doctoral education and dissertation work effectively assisted with further development and application of TIW into various research settings.
As seen in Sections 4.1.3 and 4.2.3 and noted in Sections 5.1 and 5.2, TIW exhibits theoretical amicability. Theoretical amicability is exhibited by TIW’s versatility to be used alongside other theories or theoretical concepts as well as to inform or guide the development of other concepts, models, or theories. Pang et al. (2020) combine Burnett (2015)’s expanded TIW with activity theory to better understand the information worlds of seniors during natural disasters, identifying significant roles of individual and social factors as well as the influence of space, proximity, and technology. In their conclusion, Pang et al. (2020, p. 629) argue that “[d]rawing on concepts from activity theory with the TIW allowed us to seek out substantial connections between information worlds and purposeful activities.”
Blending methodological and theoretical versatility, TIW was also combined with grounded theory approaches. As stated by Gibson and Kaplan (2017, p. 133), “Because this theory [TIW] is not predictive or prescriptive at the level of specific populations, it does not violate Corbin and Strauss (2014)’s or Charmaz (2014)’s suggestion that initial grounded theory should not test the validity of currently existing theoretical frameworks.” As noted in Section 2.2, TIW has no official propositions and is not intended to be predictive. Even though Park (2022) noted that the lack of official propositions could be considered a weakness, the omission appears to further support TIW’s strengths in methodological flexibility and theoretical amicability. Contrarily, the development of propositions may encourage more TIW use with quantitative methods.
5.4. Weaknesses: Social vs. Individual Information Worlds
As noted in Sections 4.2.2 and 5.2, Yu (2012) offers the most direct challenge to TIW with their introduction of the information worlds of individuals, arguing that Burnett and Jaeger’s formulation of information worlds does not adequately account for individual agency and other personal factors. However, Yu (2012) notes that issues related to parsing social and individual information worlds, the formation of information worlds, and understanding how information worlds impact or interact with society remain. Yu (2012, p. 16) acknowledges that continued research and development of Burnett and Jaeger’s TIW, or those developed by others, may address such issues. Burnett (2015)’s later integration of the domain of the individual simultaneously addressed prior limitations identified by Yu (2012) as well as potentially anticipated calls from Worrall et al. (2021) to integrate emotional or affective factors into social information behavior theory and research. Further, the domain of signification may account for Jaeger et al. (2014)’s suggested sixth core concept of bridges. Burnett (2015)’s added domain of signification focuses on the signs, languages, tools, and technologies that may or may not enable the exchange of information in a way similar in intent to the concept of bridges, which focuses on the ways in which information may or may not be moved across boundaries. However, broader adoption of the bridges concept is outside the scope of this project and may warrant further research.
The ability of the revised TIW, Burnett (2015)’s information domains framework, to address these concerns also requires further exploration. Within this study’s sample, just two research articles applied the information domains framework: Bao and Ke (2023) and Pang et al. (2020). Bao and Ke (2023) employ the concept of transition (Ruthven, 2022) alongside the expanded version of TIW (Burnett, 2015), in part to overcome the perceived social focus of TIW and to better understand how an individual’s cognitive, emotional, and physiological factors and activities impact information behavior during different stages of a transition process. In their study, the transitions were focused on the changing information worlds through different phases of lockdown as experienced by depression patients during the COVID-19 pandemic. Bao and Ke (2023, p. 983) note in their conclusion that they “understand the effect of emotion, body, and embodiment in crisis situations on individual meaning construction as a motivating factor for individuals to create a picture of the information worlds and the ongoing impact it is thought to have on individuals’ lives.” Additionally, Pang et al. (2020) specifically note that the combination of activity theory (Engeström, 1987) and TIW’s domain of the individual helped them understand not just the social contexts of behaviors, but also the individual characteristics that could influence individuals’ information behaviors “rather than treating the subject as a black box” (Pang et al., 2020, p. 628). With some additional conceptual and theoretical support, the expanded TIW shows some potential in overcoming the limitations stated by Yu (2012), though more work is needed to explore the applications and developments of Burnett (2015)’s expanded TIW framework. TIW’s theoretical amicability allows it to work alongside other concepts, models, and theories in cooperative and constructive ways.
Although not in the sample of this or the previous study, Savolainen (2021) briefly discusses TIW in relation to three levels of critique for the purposes of developing theoretical concepts and models of human information behavior. Savolainen (2021) argues for three distinct levels of critique based on depth: the lowest level focusing on gaps or absences in the research literature; the middle level focusing on finding and interpreting limitations of existing theories; and the highest level that addresses identified limitations by proposing alternatives or modifications to strengthen human information behavior theories. Savolainen (2021) positions TIW in the second level, arguing that TIW’s development, as described in Burnett and Jaeger (2008; 2011), is based on a critique of the scope of Chatman (1999; 2000)’s small worlds theories due to their inability to address interactions between other small worlds and societal worlds. However, using Savolainen’s levels of critique, it seems like TIW should fall into the third level, as Burnett and Jaeger’s initial development of TIW builds on the limitations of small worlds through modification of the information value concept and expansion through the addition of the concept of boundaries, and not on critique without proposed solutions. Burnett (2015)’s later development of TIW into the information domains framework also features constructive criticism through the integration of domains to strengthen the theory by addressing weaknesses, such as those identified by Yu (2012). However, Savolainen (2021) did not capture these developments.
5.5. Emergent Themes, Limitations, and Future Work
The primary emergent themes of this study are largely represented by the strengths and weaknesses identified in Sections 5.3 and 5.4. Themes regarding TIW’s use across myriad research contexts, methodological flexibility, and theoretical amicability are meaningful, but are not unexpected. In fact, these strengths align with Jaeger and Burnett (2010)’s original intentions for the theory to be useful in these ways. The results of this study provide some evidence to support those intended goals. These features may explain TIW’s steady adoption. However, this study is not equipped nor intended to compare TIW with other social information behavior theories or to compare the adoption rate of TIW with related theories. Foundational TIW texts, such as Burnett and Jaeger (2008) and Jaeger and Burnett (2010) provide more information on the development and context of TIW. A larger, more recent, and comprehensive data set is needed to compare TIW’s adoption rate with other related theories.
TIW’s focus on social contexts at the perceived expense of individual cognitive and affective factors emerged as the primary weakness, with Yu (2012)’s direct challenge as well as the indirect critiques from Jaeger et al. (2014)’s introduction of the bridges concept and Worrall et al. (2021)’s calls for a socio-emotional paradigm shift. Burnett (2015)’s introduction of the information domains framework seems to address these concerns. The domain of the individual can account for an individual’s agency as well as cognitive and affective factors. The domain of signification, which focuses on the tools, technologies, symbols, and languages that facilitate the use and exchange of information, seems to account for the concept of bridges, which focuses on how information is exchanged across boundaries. As stated in Section 5.4, although two studies in this sample (Bao & Ke, 2023; Pang et al., 2020) reported useful applications of information domains, further research is needed to explore the use of the information domains framework to assess whether the framework addresses TIW’s weaknesses. Similarly, future work could explore the impact or use of the bridges concept as well.
Some uses and interpretations of TIW that emerged during the analysis related to these larger themes are interesting. In particular, and as noted above, Gibson (2016) and Gibson and Kaplan (2017) used TIW in their grounded theory studies because TIW is not prescriptive. This is an interesting finding because early grounded theory work by Glaser and Strauss (1967) and later Glaser (1998), specifically, discourages the use of pre-existing theories for coding and encourages delaying explorations of related research literature until near the end of data analysis (Thistoll et al., 2016; Thornberg, 2012). However, Gibson (2016) and, in later work, Gibson and Kaplan (2017) use a relatively more recent, post-positivist or constructivist form of grounded theory drawing from Charmaz (2014) and Corbin and Strauss (2008). See Thistoll et al. (2016), Thornberg (2012), and Kelle (2007) for more on the development and differentiation of grounded theory. As noted in Section 2.2 and discussed in Section 5.3, TIW’s lack of propositions is an apparent strength that permits TIW to be used with various methods and alongside other theories.
Even though TIW has been used to study a variety of research populations, few studies seem to focus on libraries, librarians, library educators, or other information professionals. Froggatt (2015)’s work demonstrates how TIW can be helpful for understanding how IU students benefit from access to school librarian programs. Jaeger et al. (2014) argue that the concepts of TIW alongside the introduced concept of bridges may help librarians and libraries to better understand and perform their intermediary roles in supporting access and use of e-government resources and the challenges faced by their library users in terms of information value, boundaries, and bridges. One of the studies included in this sample, Hollister (2020), is based on a portion of his dissertation research (Hollister, 2016), which explores the interactions between the core concepts of TIW and digital literacies. Hollister (2016) argues that social types, social norms, and information values can impact an individual’s information behaviors and digital literacy practices, such as which sources of information are considered important and how to appropriately use information within a community based on its social norms and information values. Considering practical implications, Hollister’s findings suggest that librarians and library educators should consider social types, social norms, and information value systems when engaging in information and digital literacy instruction and developing curricula. The social norms and information values of an information world may enable or hinder the effectiveness of its members’ information or digital literacy skills or acceptance of information from outside sources.
Building on those implications, a stronger understanding of a community’s social types, social norms, information behaviors, information value systems, and boundaries could help libraries and librarians be more effective with community outreach, programming, and instruction. TIW may also be a useful tool for librarians and libraries to assess and meet the needs of diverse communities, creating more inclusive and representative collections, services, and staffing. Future work on TIW should explore the potential applications in professional practice in libraries, archives, schools, universities, and other settings.
The design of this study introduces limitations as well. The small sample size could be augmented by including more languages beyond English and Korean, including more paywalled academic databases not currently available to the research team, and exploring TIW use in other publication formats, such as conference proceedings, books and book chapters, dissertations and theses, and grey literature. Interviews or focus groups conducted with scholars who have used or are using TIW might provide additional insight and depth not captured in the articles.
Given the findings, themes, and limitations of this study, the researchers propose several areas of future research and work:
(1) Continued application, development, and testing of TIW across new research contexts and more methods. Although TIW is amethodological, it is primarily used with qualitative methods. More quantitative and mixed methods studies using TIW may aid in adoption and development.
(2) Broader explorations and comparisons of TIW with other LIS theories. The findings of this study suggest that TIW plays well with a variety of methods and with other theories, and can be used to inform new concepts and theories, yet awareness and use of TIW seem to be comparatively low. The relationship of TIW to other theories and its overall impact on LIS scholarship could be explored and evaluated in the future. Relatedly, future systematic reviews of TIW could expand their scope to include more theories, more articles in other databases, other publication types, additional languages, etc. as well as conducting bibliometric or scientometric studies to examine comparative use and citation rates, research trends, interdisciplinarity, and the evolution of theory use in LIS more broadly.
(3) Exploration and description of the application and development of TIW, its core concepts, and expansions. Burnett (2015)’s information domains framework and Jaeger et al. (2014)’s concept of bridges seem to be the primary theoretical developments of TIW. Future work could explore and assess the use of these revisions or expansions to TIW and whether they improve upon TIW’s strengths, and address its weaknesses.
(4) Application of TIW to inform professional LIS practice and education. Given TIW’s strengths, it may be a useful tool in professional LIS and educational settings, such as libraries, archives, and other information organizations. TIW may aid libraries, librarians, and other information professionals in building and providing inclusive, equitable, and socially just collections, services, instruction, outreach, policies, and staffing that are responsive to and representative of the information worlds of the diverse communities they serve. More work is needed to explore the practical applications of TIW, to evaluate its use as a tool for working professionals as well as its usefulness in preparing future librarians, archivists, and other information professionals.
6. CONCLUSION
Through directed qualitative content analysis, this study expands on the findings from a systematic review (Park et al., 2022) on the use of TIW in peer-reviewed research articles with qualitative exploration of the ways TIW has been applied, developed, and discussed. The findings of this study provide further context into how and why TIW is being used. TIW’s strengths in its abilities to be useful for understanding and interpreting complex, multi-level sociotechnical research contexts, its (a)methodological flexibility, and its robustness when used as a primary theoretical framework, as well as its theoretical amicability to mesh with other concepts, models, and theories have all encouraged and supported its continued use and development. These core findings provide support for and align with the original intentions of TIW as specified by Burnett and Jaeger (2008) (Jaeger & Burnett, 2010). TIW is also shown to be useful for advancing the development of new context-aware concepts and theories. Despite criticisms of TIW’s emphasis on social aspects over individual factors (Yu, 2012), Burnett (2015)’s integration of the domain of individuals may address this concern as well as more directly acknowledge or address cognitive and emotional factors, as promoted by Worrall et al. (2021). The domain of signification may also account for Jaeger et al. (2014)’s proposed sixth core concept of bridges.
Exploration and evaluation of the continued use and development of TIW is warranted in future research. Introduced originally in 2008, TIW is a relatively young theory and its use is likely to grow over time. Circling back to review its use and growth in another decade or two may reveal new insights. Future work should also consider the adoption and application of Burnett (2015)’s information domains framework. Regardless of its sole focus on TIW, this study also demonstrates that theory use and development exist within LIS. In turn, the research team echoes calls from other scholars to promote theory application and development in LIS. The research team hopes this study inspires interest and adoption of the TIW in the distinct, yet intrinsically connected information worlds of LIS research and professional practice, as well as across boundaries into other disciplines.
REFERENCES
, (2023) Chaos, expansion, and contraction: The information worlds of depression patients during the COVID-19 pandemic lockdown Journal of the Association for Information Science and Technology, 74, 971-989 https://doi.org/10.1002/asi.24769.
(1989) The design of browsing and berrypicking techniques for the online search interface Online Review, 13, 407-424 https://doi.org/10.1108/eb024320.
, (2009) The dark side of information: Overload, anxiety and other paradoxes and pathologies Journal of Information Science, 35, 180-191 https://doi.org/10.1177/0165551508095781.
(1980) The foundations of information science. Part I. Philosophical aspects Journal of Information Science, 2, 125-133 https://doi.org/10.1177/016555158000200302.
(2015) Information worlds and interpretive practices: Toward an integration of domains Journal of Information Science Theory and Practice, 3, 6-16 https://doi.org/10.1633/JISTaP.2015.3.3.1.
, , , (2011) New directions in information behaviour Emerald Group Publishing Limited The theory of information worlds and information behaviour, pp. 161-180, https://doi.org/10.1108/S1876-0562(2011)002011a010
, , (2013) Personal health record interfaces: A hermeneutic analysis First Monday, 18 https://doi.org/10.5210/fm.v18i8.4748.
, , (2009) Latinas cross the IT border: Understanding gender as a boundary object between information worlds First Monday, 14 https://doi.org/10.5210/fm.v14i9.2581.
, , , (2019) A team-based approach to open coding: Considerations for creating intercoder consensus Field Methods, 31, 116-130 https://doi.org/10.1177/1525822x19838237.
(1991) Life in a small world: Applicability of gratification theory to information-seeking behavior Journal of the American Society for Information Science, 42, 438-449 https://doi.org/10.1002/(SICI)1097-4571(199107)42:6<438::AID-ASI6>3.0.CO;2-B.
(1999) A theory of life in the round Journal of the American Society for Information Science, 50, 207-217 https://doi.org/10.1002/(SICI)1097-4571(1999)50:3<207::AID-ASI3>3.0.CO;2-8.
, (2008) Basics of qualitative research: Techniques and procedures for developing grounded theory (3rd ed.) SAGE Publications https://doi.org/10.4135/9781452230153
, (2006) The impact of institutional forces upon knowledge sharing in the UK NHS: The triumph of professional power and the inconsistency of policy Public Administration, 84, 1-30 https://doi.org/10.1111/j.0033-3298.2006.00491.x.
(1987) User acceptance of information systems : The technology acceptance model (TAM) https://hdl.handle.net/2027.42/35547
(2002) Information seeking and use by battered women: A "person-in-progressive-situations" approach Library & Information Science Research, 24, 343-355 https://doi.org/10.1016/S0740-8188(02)00132-9.
, , , , (2003) Handbook of the life course Springer US The emergence and development of life course theory, pp. 3-19, https://doi.org/10.1007/978-0-306-48247-2_1
(2015) The informationally underserved: Not always diverse, but always a social justice advocacy model School Libraries Worldwide, 21, 54-72 https://doi.org/10.29173/slw6883.
(2016) Building a progressive-situational model of post-diagnosis information seeking for parents of individuals with Down syndrome Global Qualitative Nursing Research, 3, 2333393616680967 https://doi.org/10.1177/2333393616680967. Article Id (pmcid)
, (2017) Place, community and information behavior: Spatially oriented information seeking zones and information source preferences Library & Information Science Research, 39, 131-139 https://doi.org/10.1016/j.lisr.2017.03.001.
(2020) The information worlds of online role-players Journal of Korean Biblia Society for Library and Information Science, 31, 223-266 https://doi.org/10.14699/kbiblia.2020.31.2.223.
, , , (2023) Collaborative codebook development across information worlds: Intersections between pedagogy, theory, and method in three dissertations Journal of Education for Library and Information Science, 64, 18-36 https://doi.org/10.3138/jelis-2020-0095.
(2018) Toward a socio-contextual understanding of transliteracy Reference Services Review, 46, 178-188 https://doi.org/10.1108/rsr-02-2018-0016.
, (2005) Three approaches to qualitative content analysis Qualitative Health Research, 15, 1277-1288 https://doi.org/10.1177/1049732305276687.
, (2001) Using everyday life information seeking to explain organizational behavior Library & Information Science Research, 23, 351-366 https://doi.org/10.1016/S0740-8188(01)00093-7.
, (2010) Information worlds: Behavior, technology, and social context in the age of the Internet Routledge. https://doi.org/10.4324/9780203851630
, , , , , , , (2014) Connecting government, libraries and communities: Information behavior theory and information intermediaries in the design of LibEGov.org First Monday, 19 https://doi.org/10.5210/fm.v19i11.4900.
, (2005) Knowledge structure of library and information science in South Korea Library & Information Science Research, 27, 51-72 https://doi.org/ .
, , (2011) Trends in information behavior research, 1999-2008: A content analysis Library & Information Science Research, 33, 19-24 https://doi.org/10.1016/j.lisr.2010.07.014.
, (2016) Applying the theory of information worlds within a health care practise in Finland Journal of Documentation, 72, 321-341 https://doi.org/10.1108/jd-05-2015-0065.
(2024) Application of theories in library and information science research in Tanzania: A content analysis Alexandria, 34, 14-27 https://doi.org/10.1177/ .
, (2006) An analysis of the development and use of theory in library and information science research articles Library & Information Science Research, 28, 548-562 https://doi.org/10.1016/j.lisr.2006.03.018.
(1991) Inside the search process: Information seeking from the user's perspective Journal of the American Society for Information Science, 42, 361-371 https://doi.org/(SICI)1097-4571(199106)42:5<361::AID-ASI6>3.0.CO;2-#.
, , (2013) Theory talk in the library science scholarly literature: An exploratory analysis Library & Information Science Research, 35, 175-180 https://doi.org/10.1016/j.lisr.2013.02.004.
(2019) An exploratory study on the political information behaviors of Korean opinion leaders on Twitter: Through the lens of theory of information worlds Journal of the Korean Society for Library and Information Science, 53, 83-108 https://doi.org/10.4275/KSLIS.2019.53.1.083.
, (2019) How are information deserts created? A theory of local information landscapes Journal of the Association for Information Science and Technology, 70, 101-116 https://doi.org/10.1002/asi.24114.
, , (2002) Content analysis in mass communication: Assessment and reporting of intercoder reliability Human Communication Research, 28, 587-604 https://doi.org/10.1111/j.1468-2958.2002.tb00826.x.
(2021) The structure of information behavior dissertations 2009-2018: Theories, methods, populations, disciplines Journal of Librarianship and Information Science, 53, 225-232 https://doi.org/10.1177/0961000620935499.
(2019) The citation impact of information behavior theories in scholarly literature Library & Information Science Research, 41, 100981 https://doi.org/10.1016/j.lisr.2019.100981.
, (2021) Access to information on family planning (FP) methods among married women of reproductive age in Ilala district, Dar es Salaam Tanzania University of Dar es Salaam Library Journal, 16, 98-114 https://doi.org/10.4314/udslj.v16i1.
(2019) Linkages between information overload and acculturative stress: The case of Black diasporic immigrants in the US Journal of Librarianship and Information Science, 0961000619857115 https://doi.org/10.1177/ .
(2020) Toward a new understanding of immigrant information behavior: A survey study on information access and information overload among US Black diasporic immigrants Journal of Documentation, 76, 869-891 https://doi.org/10.1108/jd-04-2019-0066.
, (2010) Turning weakness into strength: Strategies for future LIS Journal of Documentation, 66, 7-27 https://doi.org/10.1108/00220411011016344.
, (2019) Small worlds in a distant land: International newcomer students' local information behaviors in unfamiliar environments Journal of the Association for Information Science and Technology, 70, 1060-1073 https://doi.org/10.1002/asi.24185.
, , (2020) Exploring the information worlds of older persons during disasters Journal of the Association for Information Science and Technology, 71, 619-631 https://doi.org/10.1002/asi.24294.
(2022) A reflection on social perspective of information behavior: Around the theory of information worlds Journal of the Korean Society for Library and Information Science, 56, 425-447 https://doi.org/10.4275/KSLIS.2022.56.1.425.
, , (2022) A systematic review on the application of the theory of information worlds Journal of Information Science Theory and Practice, 10, 87-109 https://doi.org/10.1633/JISTaP.2022.10.4.7.
, (2001) The use of theory in information science research Journal of the American Society for Information Science and Technology, 52, 62-73 https://doi.org/10.1002/1532-2890(2000)52:1<62::AID-ASI1061>3.0.CO;2-J.
, , (2022) When politicians and the experts collide: Organization and the creation of information spheres Journal of the Association for Information Science and Technology, 73, 1127-1139 https://doi.org/10.1002/asi.24618.
, (2025) Disconnected and disabled during the pandemic: Toward more inclusive pandemic response plans in the Global South Journal of Librarianship and Information Science, 57, 211-222 https://doi.org/10.1177/09610006231207657.
(2009) Constructs, measurements and models of acculturation and acculturative stress International Journal of Intercultural Relations, 33, 106-123 https://doi.org/10.1016/j.ijintrel.2008.12.001.
(2022) An information behavior theory of transitions Journal of the Association for Information Science and Technology, 73, 579-593 https://doi.org/10.1002/asi.24588.
(2021) Levels of critique in models and concepts of human information behaviour research Aslib Journal of Information Management, 73, 772-791 https://doi.org/10.1108/ajim-01-2021-0028.
, , (1989) Distributed artificial intelligence Morgan Kaufmann The structure of Ill-structured solutions: Boundary objects and heterogeneous distributed problem solving, pp. 37-54, https://doi.org/10.1016/B978-1-55860-092-8.50006-X
, (1989) Institutional ecology, 'translations' and boundary objects: Amateurs and professionals in Berkeley's Museum of Vertebrate Zoology, 1907-39 Social Studies of Science, 19, 387-420 https://doi.org/10.1177/030631289019003001.
(1987) Qualitative analysis for social scientists. Cambridge University Press https://doi.org/10.1017/CBO9780511557842
, , (2016) Acquiring and developing theoretical sensitivity through undertaking a grounded preliminary literature review Quality & Quantity, 50, 619-636 https://doi.org/10.1007/s11135-015-0167-3.
(2012) Informed grounded theory Scandinavian Journal of Educational Research, 56, 243-259 https://doi.org/10.1080/00313831.2011.581686.
, (2021) To borrow or not to borrow is the question? Theory borrowing in library information science postgraduate research in Nigeria and South Africa The International Information & Library Review, 53, 48-62 https://doi.org/10.1080/10572317.2020.1790261.
, , (2022) Disciplinary contributions to research topics and methodology in library and information science-Leading to fragmentation? Journal of the Association for Information Science and Technology, 73, 1706-1722 https://doi.org/10.1002/asi.24690.
, , , (2022) Theory usage in empirical research in ISIC conference papers (1996-2020) Information Research, 27, isic2227 https://doi.org/10.47989/irisic2227.
, , , (2003) User acceptance of information technology: Toward a unified view MIS Quarterly, 27, 425-478 https://doi.org/10.2307/30036540.
(2019) Circling the reality of public institutions: An e-Delphi study of information, culture, and community stakeholders voicing the way forward in Detroit, Michigan Libri, 69, 241-261 https://doi.org/doi:10.1515/libri-2019-0108.
(1998) Communities of practice: Learning, meaning, and identity Cambridge University Press https://doi.org/10.1017/CBO9780511803932
, , (2015) The unified theory of acceptance and use of technology (UTAUT): A literature review Journal of Enterprise Information Management, 28, 443-488 https://doi.org/10.1108/jeim-09-2014-0088.
(1999) Models in information behaviour research Journal of Documentation, 55, 249-270 https://doi.org/10.1108/eum0000000007145.
(2019) "Connections above and beyond": Information, translation, and community boundaries in LibraryThing and Goodreads Journal of the Association for Information Science and Technology, 70, 742-753 https://doi.org/10.1002/asi.24153.
, , (2021) The importance of socio-emotional considerations in online communities, social informatics, and information science Journal of the Association for Information Science and Technology, 72, 1247-1260 https://doi.org/10.1002/asi.24489.
, , , (2021) How do mothers exchange parenting-related information in online communities? A meta-synthesis Computers in Human Behavior, 115, 106631 https://doi.org/10.1016/j.chb.2020.106631.
(2012) Towards a reconceptualization of the 'information worlds of individuals' Journal of Librarianship and Information Science, 44, 3-18 https://doi.org/10.1177/0961000611424586.
- Received
- 2025-05-14
- Revised
- 2025-06-26
- Accepted
- 2025-07-17
- Published
- 2025-12-30
- Downloaded
- Viewed
- 0KCI Citations
- 0WOS Citations


